Security Built Into Every Layer
APIWORX enforces security at the database level, the API gateway, and the network perimeter. Tenant isolation, encrypted credentials, and real-time threat monitoring are foundational — not add-ons.
We provide full transparency to our certifications, procedures, and policies.
Security Architecture
Security is enforced at the database, API, and infrastructure level — not layered on top as an afterthought.
Encryption at Rest & In Transit
All data is encrypted using industry-standard protocols. Database records are fully encrypted at rest in managed relational storage. All network communication uses TLS 1.2+.
Tenant-Level Data Isolation
Multi-tenant architecture enforces strict data isolation at the database level using Row-Level Security (RLS) policies. Every query is automatically scoped to the authenticated tenant — no cross-tenant data access is possible.
Credential Management
API keys and secrets are hashed and encrypted at rest, isolated entirely within each tenant's specific connector instance. External API access uses scoped keys with optional expiration and revocation tracking.
Access Control & Authentication
JWT-based authentication with fine-grained role-based access controls. API keys support granular scopes (read, write, admin) and every request is validated for environment, scope, and authorization.
Security Auditing
Every API request is logged with last-used timestamps for comprehensive security auditing. Full activity logs provide end-to-end traceability for compliance and incident investigation.
Compliance
Designed to comply with privacy regulations including GDPR and SOC 2. Data handling meets legal requirements and industry standards through systematic controls and independent assessment.
API Key Gateway & Webhook Security
Every API request and inbound webhook is authenticated, validated, and logged.
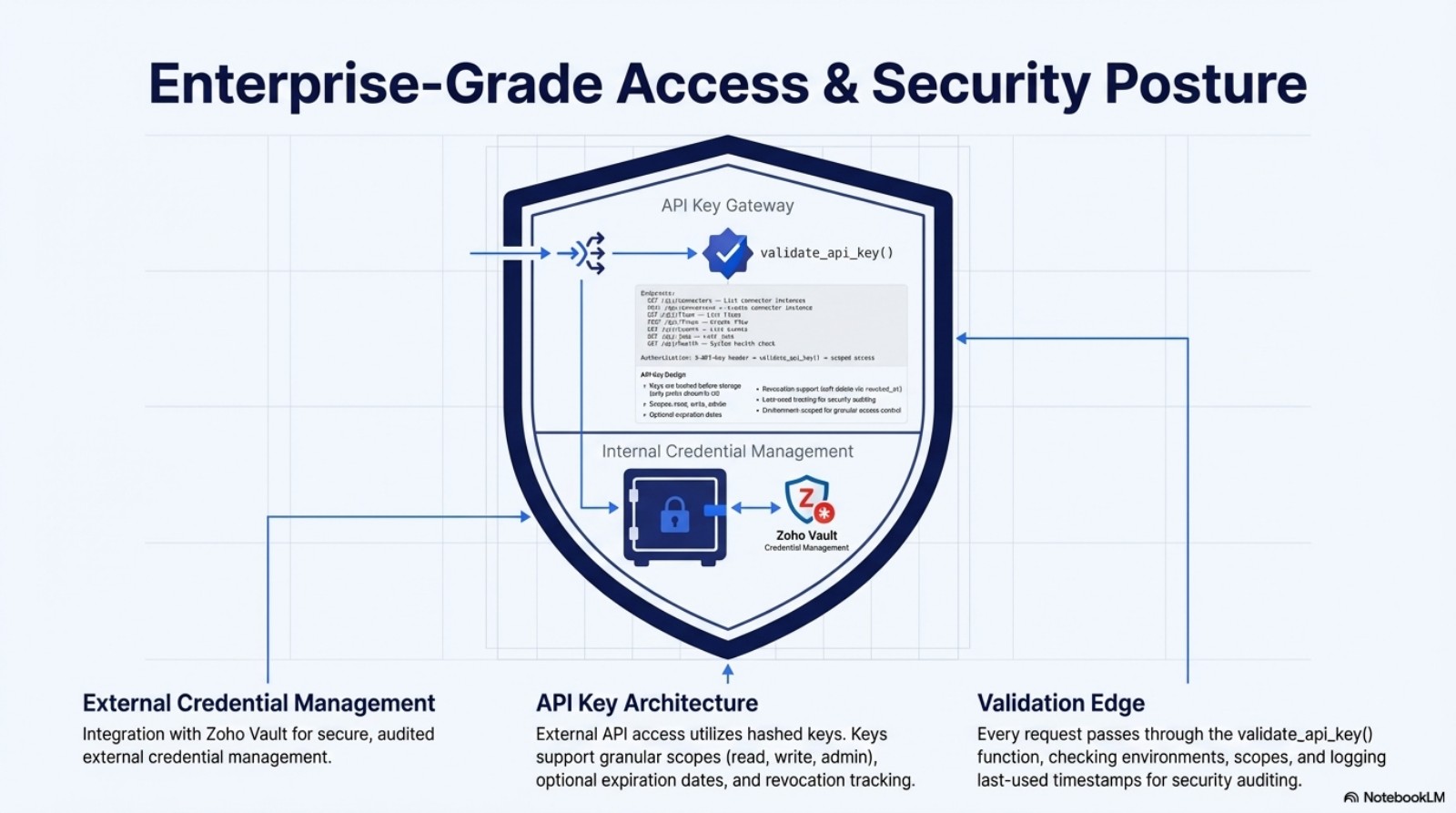
Scoped API Keys
External API access uses hashed keys with granular scopes (read, write, admin), optional expiration dates, and revocation tracking.
Request Validation
Every request passes through the validate_api_key() edge function, checking environments, scopes, and logging last-used timestamps for security auditing.
Webhook HMAC Verification
All inbound webhooks are validated against stored HMAC signatures to prevent payload tampering and replay attacks.
Environment Isolation
Resources are strictly scoped to unique environment IDs (Dev/Test/Prod). No cross-environment data leakage is possible.
Cloud Infrastructure Security
Enterprise-grade cloud infrastructure with encryption, auto-scaling, and disaster recovery.
Auto-Scaling Compute
Cloud compute environments scale dynamically based on transaction volume, running in hardened virtual environments with automatic security patching.
Encrypted Database Storage
All records are fully encrypted at rest in a managed relational database with automated failover, point-in-time recovery, and high availability.
Disaster Recovery
Near real-time snapshotting with encrypted backup records to cloud object storage. Recovery procedures are tested regularly to ensure rapid restoration.
Perimeter Security
Active server security monitoring and vulnerability scanning guard the network edge, with automated threat detection and response before attacks reach the application layer.
Active Threat Detection & Response
Multiple layers of proactive security constantly monitor and respond to threats.
Honeypots
Port Honeypot
Our system opens honeypots on randomly chosen unused ports while respecting existing services. Deep port scans are detected, exposing malicious IPs that are automatically greylisted — some honeypots behave like real services to maximize intelligence.
Web Honeypot
Works like Port Honeypot with the ability to replace compromised files with honeypot scripts. You get the same benefits plus additional customization to trap attackers and prevent further intrusion.
Intrusion Detection
Web Application Firewall
WAF constantly scans and analyzes incoming traffic for malicious content. Combined with log analysis, it provides an extremely low false-positive rate while stopping attacks against applications on your server.
Log Analysis
Continuous server log monitoring detects suspicious behavior and blocks further malicious actions. Zero-configuration setup finds logs automatically — no manual path specification required.
Malware Detection & Removal
If attackers break through honeypots and WAF, malware detection stops them from infecting your server. Removed malware is replaced with honeypots, and definitions auto-update for protection against the latest threats.
IP Reputation
CAPTCHA
Distinguishes between human and bot-generated traffic. Botnets are immediately blocked, false positives are managed automatically, and legitimate visitors can easily remove themselves from the greylist.
Collective Intelligence
Attack information is collected and shared across a global defense network that becomes more intelligent and powerful with every single attack.
IP Reputation Lists
Essential list-based protection against the most vicious IPs. When an IP generates excessive malicious requests, it's placed on the blocklist. Advanced reputation secures against millions of known attacker IPs.
DoS Protection
DoS Detection
Continuous monitoring of simultaneous incoming and outgoing connections detects Denial of Service attacks with our unique approach.
DoS Mitigation
A global defense network shares information about malicious IPs. With data on millions of IPs worldwide plus honeypots to capture the latest threats, your server is protected against DDoS botnet attacks before they happen.
AntiFlood
Prevents attackers from overloading any individual module by aggregating information from the entire security suite. No weak links in the defense chain.